Design and build your software
Technical documentation for integrating health and social care applications with CIS2 Authentication.
Overview
Integrating with CIS2 Authentication allows your software to:
- authenticate a health or social care worker, using a range of authenticators, including smartcards, Windows Hello, our iPad app and passkeys
- get the user’s personal details such as their unique ID, name and email address
- get the user’s national RBAC access permissions
- get other information about the user
- access some of our national APIs
Integrating with our APIs
If you are integrating with CIS2 Authentication to access one or more of our national APIs, follow our API security and authorisation guidance. You might end up back here depending on which integration pattern you choose.
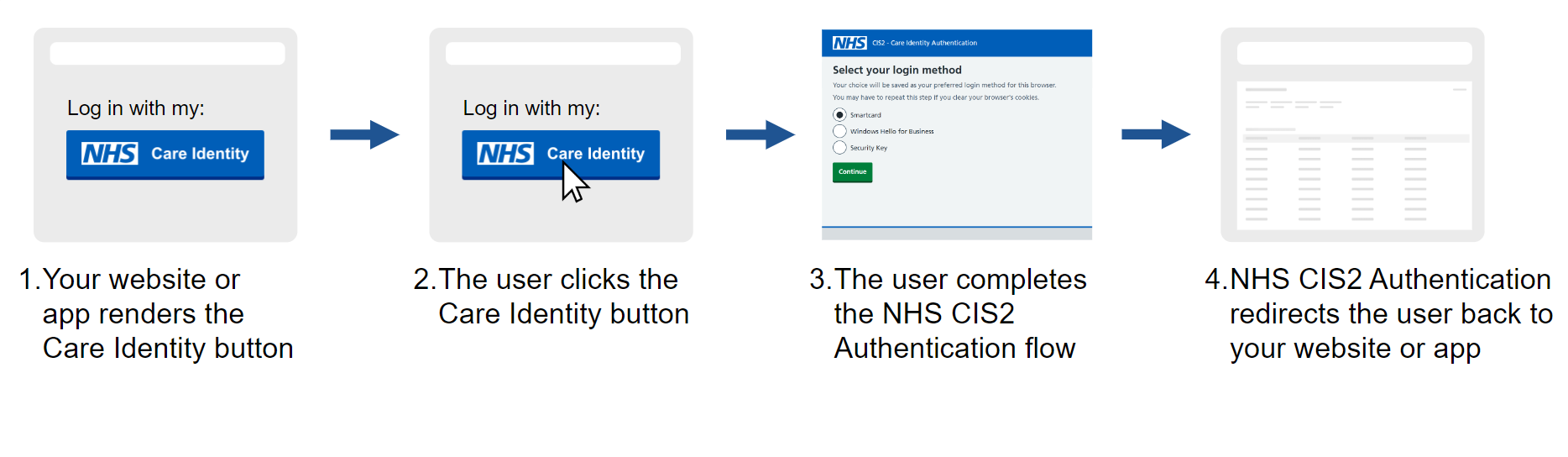
How it works
CIS2 Authentication uses the open standard Open ID Connect (OIDC).
The following sequence diagram shows how your application interacts with CIS2 Authentication:
In words:
- The healthcare worker launches the healthcare application.
- The healthcare application redirects the healthcare worker's browser to CIS2 Authentication's authentication endpoint.
- The healthcare worker signs in to their CIS account (using their chosen authenticator).
- CIS2 Authentication redirects control back to the healthcare application, with an authorisation code.
- The healthcare application calls CIS2 Authentication's token endpoint, with the authorisation code, and receives an ID token and an access token in return.
- Optionally, the healthcare application calls CIS2 Authentication's user info endpoint, with the access token, and receives the healthcare worker's user information in return.
CIS2 Authentication is primarily intended to be used with browser-based applications, but it can also be used with native desktop and mobile applications.
Further information
The following guides cover specific topics that are referenced from one or more of the build steps.
| Scopes and claims | A detailed description of the scopes and claims supported by CIS2 Authentication. |
| Authenticators | How to manage the authentication methods supported by CIS2 Authentication. |
| Key management | How to manage keys when using JSON Web Signatures. |
| Security considerations | Security considerations when using CIS2 Authentication and specific TLS requirements. |
| Role selection | How to select and change the user's national RBAC role using CIS2 Authentication. |
| Native applications | OIDC Authorisation Code Flow is primarily a browser-based standard, but it's also possible to use it in native desktop and mobile applications. |
Next steps
Once you've designed and built your integration, the next step is to test your software.
Last edited: 17 March 2026 10:07 am
